I’ve recently had a horrible bout of spam bots attacking CreativeJS.com, so I thought I’d write a (rather mundane but hopefully useful) post about what I’ve done to combat them, as much to serve as a reminder to myself as much as anything.

Robot attack by flickr.com/donsolo
TL;DR
Install Anti-spam plugin
Install All in One WP Security plugin
Check your log files and add malicious IP addresses to iptables
I moved all my hosting to Linode a few months ago – it’s been a steep learning curve understanding how to run a Linux server, but I’m glad that I got here. Don’t get me wrong – I love a GUI, but there’s also something I really like about low level command line access. I’m not sure what – maybe it’s just because my early computing experiences were so low-level.
Thanks to the excellent Linode tutorials (and help from CreativeJS team member Paul King) I’d got the server up and running, but I found that I kept getting intermittent outages – page requests were timing out (thanks to the free website monitoring tools Pingdom and StatusCake). It seemed like there were too many people accessing my pages, but Google analytics wasn’t reporting unusually high traffic.
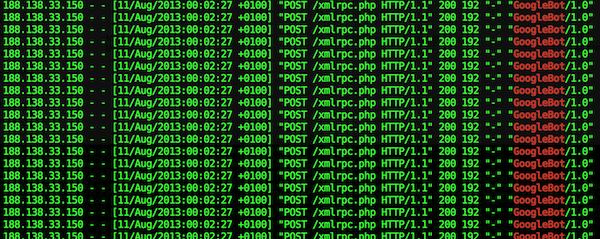
Investigating the access logs I noticed multiple requests for the xmlrpc.php file. I think that this file provides an API for external applications to interface with WordPress, even allowing you to add comments – hence the reason why we were getting hundreds of spam comments.
Akismet was catching them, but I installed the Anti-spam plugin for WordPress which stopped them all dead. It was brilliant.
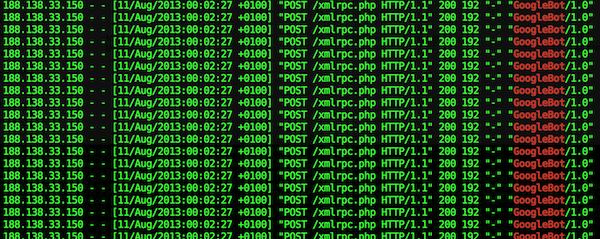
But I was still getting hundreds of requests for xmlrpc.php and it was clogging my sites up. The access logs showed that the client was purporting to be the “GoogleBot/1.0”, but I confirmed that it wasn’t using the method outlined on this Google Webmaster Central blog post.
I initially blocked the IP address in my apache httpd.conf file, which stopped the bot accessing the file, but at this point it was making around 50 attempts per second and my log files were getting so large that my server hard disk space had run out!
So I also added the malicious IP addresses to iptables which stopped the bots getting to my server at all, at least it was no longer registering in my access logs.
Finally I installed the amazing All In One WP Security and Firewall plugin which so far seems amazing, and probably renders my messing around with iptables and httpd.conf unnecessary.
So far the server seems a lot happier, it certainly feels good that I’m starting to get a grip on this sysadmin stuff!

One reply on “Securing my WordPress sites”
As always, very helpful article. Actually running some smaller websites on WP as well and this helped me a lot, because recently the spam got annoying as well.
thanks a lot!
M